Tl;dr: We’re going to collect metadata on Easterhegg 2019 to improve DECT device compatibility. All collected data will be deleted after a 4 month period. No Voice will be captured.
Why?
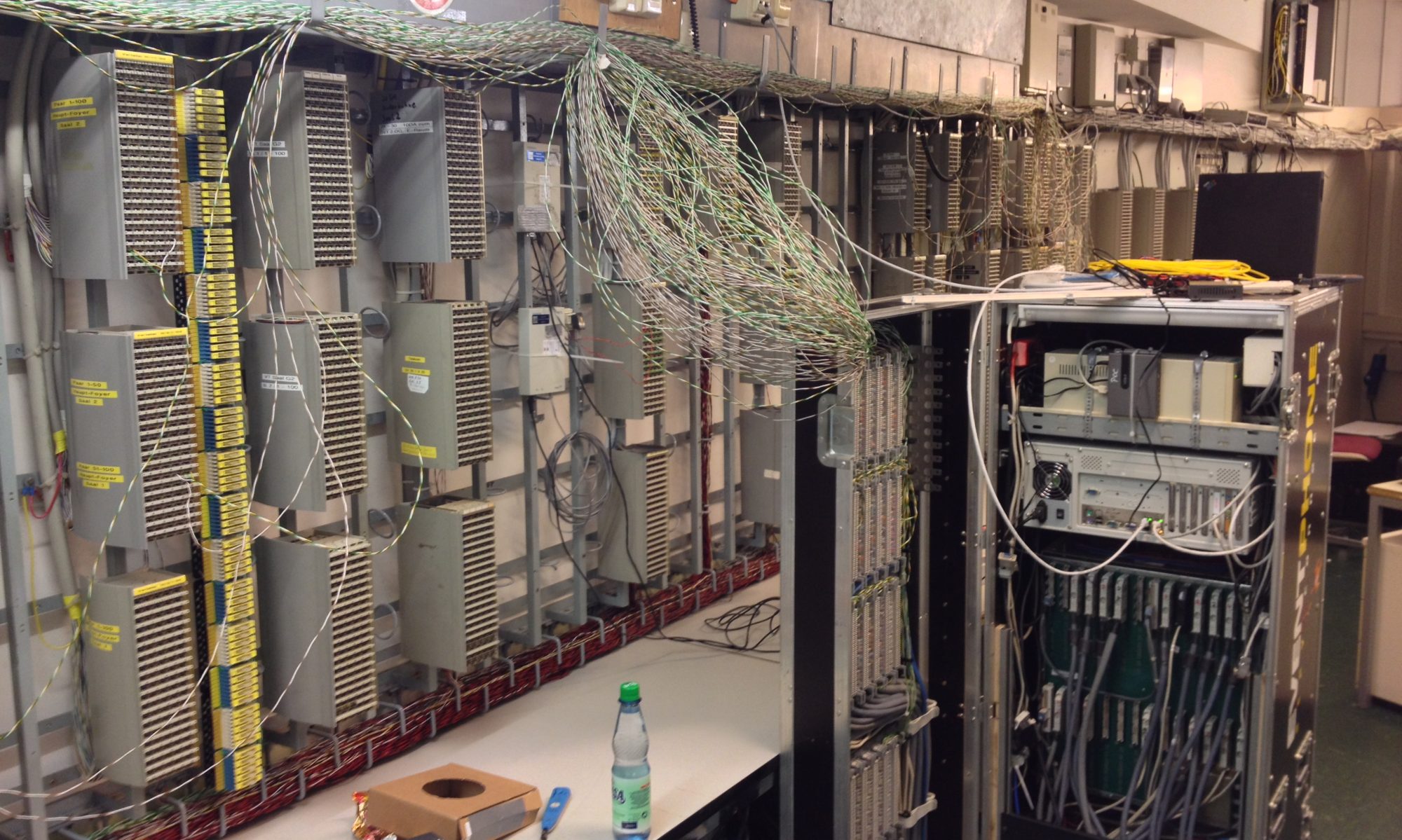
Last year, we almost completely replaced the Phone Operation Center (PoC) hardware and software, making it easier to use. This has given us the opportunity to provide functionality that was impossible to implement with our old setup. This includes self-registration of DECT phones, better extendability, self-administration of extensions and call groups and the LDAP phonebook. Now we want to solve another major problem from the user’s point of view. The compatibility of DECT devices. DECT-GAP is a standard which allows free interpretation of some parts. As a result, there is a considerable number of devices that do indicate DECT-GAP conformity in their datsheets, but still do not work at all or only with restrictions on our system. Up to now, no manufacturer has been willing to ensure that the devices work with our system, e.g. through firmware adaptations, even though we have made concrete suggestions for changes that wouldn’t have caused disadvantages with regard to compatibility with their own base stations.
In our test system, we were able to analyze and understand the communication of some devices that had not worked before. We have adapted our system so that it recognizes some of these models by making the required information available to them. With other models, we still don’t have enough information to guarantee reproducible and reliable connections. There are also models where we don’t even know why they don’t work.
We like to get a deeper insights of the DECT infrastructure when many different models from different vendors are registered. (Perhaps) This will enable us to support a greater variety of DECT devices. The basis for this is an understanding of how different devices communicate on the DECT interface. Therefore, we need significantly more sample data than what we can produce by manual tests. Since we do not store any connection data, we are not able to analyze data from past events. Because of this, we want to store connection data on the Easterhegg 2019.
Currently we have not found a way to offer opt-in on a per user basis. We could not answer many questions such as: “What do we do if a participant agrees to capture the data and calls a participant who has not agreed?”; “What happens with a group call where some members have agreed and some have not?”. If we optionally anonymize data per user, you can still see who tried to call from the call setup and you have to delete the attempted call setup for the user who tried to call and vice versa. Since we know that it is basically bad to store data, we have come to the conclusion that the situation doesn’t get any better if we make users believe that it’s safe to click on a checkbox when we can’t make sure it will work. We have decided to make transparent what we intend to do with the data, store it in a responsible way and to delete it safely after a specified period of time. If you do not want your metadata to be stored, you must not use any of our extensions on Easterhegg 2019. We believe that, unlike a Congress or Camp, this is acceptable on an Easterhegg.
What data is affected?
It is basically about the metadata of the DECT extensions. Speech/Voice data is not stored. The control messages between the antennas and the central software component that coordinates the antennae and phones are affected.
In detail, these are the following data:
- the identities of the DECT devices: IPEI, TPUI and IPUI,
- the keys used to encrypt the calls,
- the call setup: Caller and called party
- the call end (duration),
- The mobile device details (capabilities of the mobile device),
- the keystrokes on the device (for some devices),
- the accesses to the phone book (for some devices).
Example: We store when Alice called Bob, how often it rang, how long the call lasted, what device Alice used, which device Bob used, what was shown on the displays and that during the call e.g. key 2 was pressed. This includes all data necessary to set up and disconnect the call as well as the base stations involved.
We do not evaluate keystrokes and accesses to the phone book, but we cannot rule out that this information will be sent.
Where is the data stored and how?
For the Easterhegg, we will take the server to a secure data center. The collected metadata is stored encrypted. Access to the data is exclusively encrypted. The data is explicitly excluded from all backups.
How long is the data stored?
The metadata of Easterhegg 2019 will be stored for a maximum of 4 months, i.e. until 23.08.2019 (end of CCCamp 2019). By 25.08.2019 at the latest, the data will be deleted and the area overwritten. We will officially announce the deletion.
Can I make a phone call without saving the metadata?
Yes, if you use a SIP extension and call another SIP extension, no metadata will be stored. However, you cannot ensure that a user has not converted a SIP extension into a DECT extension or group at short notice. So you have to check if the extension you want to call is a SIP extension at the moment.
Can I use the services of the PoC anonymously?
Yes, you can register with fantasy names and anonymous e‑mail addresses. We will then have the metadata, but we won’t be able to assign it to a real person. Note, however, that you are not using the phone at the camp (or 35C3) with a real name, because then we would be able to merge the data using the IPEI (we don’t intend to).
Do I have a right to information?
Yes.
If you have any questions about the procedure or data protection, please do not hesitate to contact us. You can find contact possibilities here: https://guru3.eventphone.de/support/
Our voluntarily appointed data protection officer is:
Stephan Kambor
Nobistor 40
22767 Hamburg, Germany
E‑Mail: st ‘at’ eventphone.de
DECT on Events: 2078 (20ST)
Thomas ist Eventphone Fullstack Entwickler und gehört seit Jahren zum Team. Er liefert aber nicht nur Code und administriert das Blech, sondern ist auch im Kundensupport, der Logistik, im Backoffice sowie im Marketing und der “Unternehmenskommunikation” aktiv.